Stolen Crypto Recovery in 2026: Proven Methods That Works.
Are Crypto Recovery Services Legit or Another Scam? The Truth in 2026.
Cryptocurrency scams now cost victims billions of dollars annually from fake investment platforms and wallet hacks to phishing drains and romance fraud.
After losing funds, most people search:
Can crypto recovery services really get my money back?
The answer is yes — some are legitimate forensic specialists but many others are secondary scams targeting desperate victims.
This authoritative guide explains:
✔ How real crypto recovery works
✔ How scammers fake recovery services
✔ When recovery is actually possible
✔ How to choose a legitimate provider
What Legitimate Crypto Recovery Services Actually Do

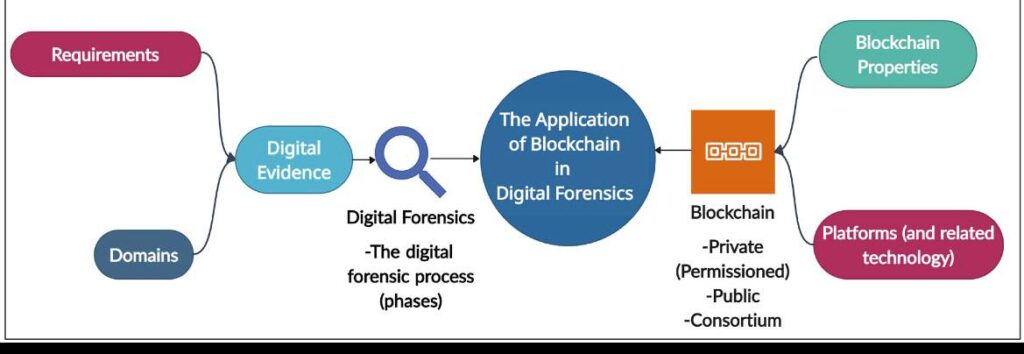
Real recovery firms rely on blockchain forensics — not hacking.
Their investigative process includes:
• Tracing stolen crypto across blockchain ledgers
• Identifying scam wallet networks
• Monitoring exchange cash-out points
• Producing forensic transaction reports
• Supporting asset freezes & legal recovery
Because blockchains are permanent public ledgers, every transaction leaves evidence.
🚨 Why So Many “Recovery Services” Are Actually Scams
Crypto fraud created a second crime wave: fake recovery agents.
Common tactics include:
❌ Guaranteed full recovery
❌ “Secret hacking tools” claims
❌ Upfront unlock fees
❌ No forensic reports
❌ Fake testimonials
❌ Pressure tactics
Important truth:
No one can reverse blockchain transactions instantly.
Recovery requires forensic tracing and exchange intervention.
How Professional Crypto Recovery Works Step-by-Step
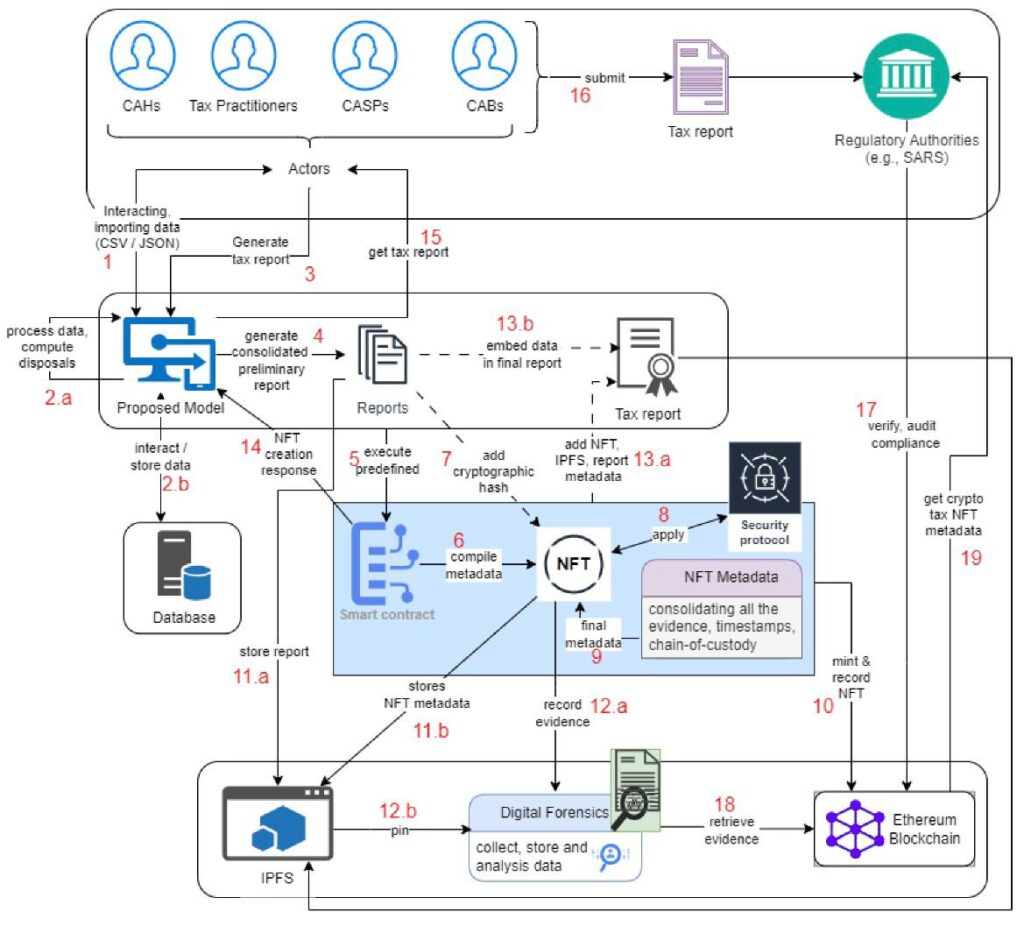
- Blockchain Transaction Mapping
Investigators reconstruct every transfer from the victim’s wallet.
This reveals:
- Receiving wallets
- Transfer chains
- Holding addresses
- Exchange deposits
- Criminal Network Analysis
Forensic software identifies:
- Linked wallets
- Reused scam addresses
- Laundering behavior
- Fraud clusters
Often exposing full operations.
- Exchange Monitoring & Asset Freezes
When funds reach exchanges:
- Evidence is submitted
- Assets are flagged
- Freeze requests initiated
- Recovery negotiations begin
- Legal-Grade Evidence Reports
Used for:
- Exchange disputes
- Law enforcement
- Civil recovery cases
📈 When Crypto Recovery Has the Highest Success Rate
Recovery works best when:
✅ Tracing begins quickly
✅ Funds reach centralized exchanges
✅ Public blockchains were used
✅ Forensic professionals are involved
Most recoverable scams include:
• Fake investment platforms
• Phishing drains
• Romance scam transfers
• Rug pull tokens
• NFT theft
• Wallet malware
A Legitimate Forensic Recovery Example
One professional service specializing in blockchain investigations is Private-Hackers.com.
They provide:
✔ Advanced blockchain tracing
✔ Scam network analysis
✔ Forensic documentation
✔ Exchange intervention
✔ Strategic asset recovery
They assist victims of:
• Crypto investment scams
• Wallet hacks
• Romance fraud
• NFT theft
• Insider crypto theft
• Rug pulls
Their success comes from evidence-based recovery not false promises.
✅ Legit Recovery Service Checklist (Save This)
Trustworthy Services:
✔ Show transaction tracing
✔ Provide forensic reports
✔ Explain recovery limits
✔ No guarantees
✔ Transparent process
Fake Services:
❌ Instant recovery claims
❌ Hacking promises
❌ Upfront unlock fees
❌ No proof of tracing
❌ Pressure tactics
🔎 Can You Track Stolen Crypto Yourself?
You can view transactions using blockchain explorers — but:
- Criminal networks are complex
- Laundering hides trails
- Exchanges require formal evidence
Professional forensic tools dramatically improve recovery outcomes.







🇨🇦 Canada — Olivia Chen, Vancouver
After losing CAD 62,000 to a fake crypto investment platform, I felt completely powerless. The scammers routed my funds through multiple wallets, making it seem impossible to trace. Private-Hackers.com performed a blockchain forensic analysis and identified a cash-out point at a regulated exchange. Their report helped authorities freeze part of the funds. I recovered about 40% — far more than I thought possible. Their professionalism restored my trust in cybersecurity services.
🇬🇧 UK — Oliver Grant, London
A supplier impersonation scam deceived our finance department into authorizing a significant USDT payment to a fraudulent wallet. The attackers had replicated legitimate email threads and payment instructions, making the request appear completely authentic. Private-Hackers.com responded promptly, conducting an in-depth blockchain trace that uncovered links to a wider phishing network operating across multiple jurisdictions.
Their detailed forensic report strengthened our case with both the bank and law enforcement, while their recommendations led us to implement multi-layer payment verification, domain monitoring, and stricter approval workflows to prevent future incidents.
Australia — Rebecca Collins, Sydney
A compromised vendor email account led to a fraudulent Ethereum payment that appeared to be part of an ongoing project settlement. The communication contained accurate project references, which made the deception difficult to detect at the time. Private-Hackers.com conducted a thorough blockchain trace, following the assets through multiple wallet hops and identifying behavioral patterns linked to repeat offenders.
Their analysis reinforced our legal submission and provided clarity on how the attack unfolded. In response, we rolled out enhanced payment validation controls, strengthened vendor communication protocols, and introduced company-wide security awareness training to mitigate future risks.