How Ethical Hackers Investigate Corporate Data Breaches and Insider Threats.

In today’s digital business environment, companies rely heavily on technology to store valuable data, manage operations, and communicate internally. While these technologies improve efficiency, they also create opportunities for cyber threats. One of the most serious threats organizations face is corporate data breaches and insider threats.
When sensitive information is compromised, companies often turn to ethical hackers and digital forensic investigators to uncover the source of the breach and protect their systems from further damage. Ethical hackers use advanced cybersecurity techniques to analyze digital evidence, identify vulnerabilities, and trace suspicious activities within corporate networks.
For businesses seeking professional assistance with cybersecurity investigations, Private-Hackers.com provides specialized digital forensic and cyber investigation services designed to detect breaches, investigate insider threats, and help organizations strengthen their security systems.
What Is a Corporate Data Breach?
A corporate data breach occurs when unauthorized individuals gain access to sensitive company information. This information may include financial records, confidential business documents, intellectual property, customer databases, or internal communications.
Data breaches can occur through various methods, including:
• hacking attacks targeting corporate networks
• phishing emails designed to steal employee credentials
• malware or spyware installed on company devices
• exploitation of software vulnerabilities
• unauthorized access by insiders
Once a breach occurs, identifying the source and extent of the damage becomes a priority for the affected organization.
Understanding Insider Threats in Corporate Security
An insider threat refers to a situation where someone inside the organization misuses their authorized access to compromise company data.
Insider threats may involve:
• employees stealing confidential information
• contractors leaking company data
• staff members sharing sensitive files with competitors
• unauthorized downloading of internal documents
Because insiders already have legitimate access to systems, detecting these threats often requires specialized investigation techniques.
The Role of Ethical Hackers in Corporate Cyber Investigations
Ethical hackers are cybersecurity professionals trained to identify vulnerabilities and investigate cyber incidents legally and responsibly. Unlike malicious hackers, their goal is to protect organizations from cyber threats and strengthen digital security systems.
In corporate investigations, ethical hackers may perform tasks such as:
• analyzing suspicious network activity
• identifying security vulnerabilities
• tracing unauthorized access attempts
• recovering deleted digital evidence
• examining employee system activity
These investigations help companies determine how the breach occurred and what steps are necessary to prevent future incidents.
How Ethical Hackers Investigate Corporate Data Breaches
Professional cyber investigators follow a structured process when examining corporate data breaches.
- Initial Incident Assessment
The investigation begins with an assessment of the reported security incident. Ethical hackers analyze the circumstances surrounding the breach, including when it occurred and which systems may have been affected.
This step helps investigators determine the scope of the investigation and identify potential evidence sources.
- Digital Evidence Collection
Digital forensic specialists collect data from various sources within the company’s network, including:
• servers and databases
• employee computers and mobile devices
• email systems
• network logs
• cloud storage platforms
Preserving digital evidence is essential to ensure accurate analysis and support possible legal proceedings.
- Network Activity Analysis
Ethical hackers carefully analyze network traffic and system logs to identify unusual behavior that may indicate unauthorized access.
Examples of suspicious activity include:
• login attempts from unknown locations
• abnormal file transfers
• unusual access to confidential data
• repeated failed login attempts
By studying these patterns, investigators can identify how attackers entered the system.
- Insider Threat Detection
When insider involvement is suspected, ethical hackers review employee activity records to identify unusual behavior patterns.
This analysis may include:
• examining file access logs
• reviewing data download histories
• analyzing communication records
• monitoring unusual system usage
These digital footprints often reveal whether an employee or contractor may have misused their access privileges.
- Data Recovery and Evidence Reconstruction
In some cases, attackers attempt to erase evidence by deleting files or modifying system records. Digital forensic experts use specialized tools to recover hidden or deleted data.
Recovered information helps investigators reconstruct the sequence of events that led to the breach.
- Identifying the Source of the Breach
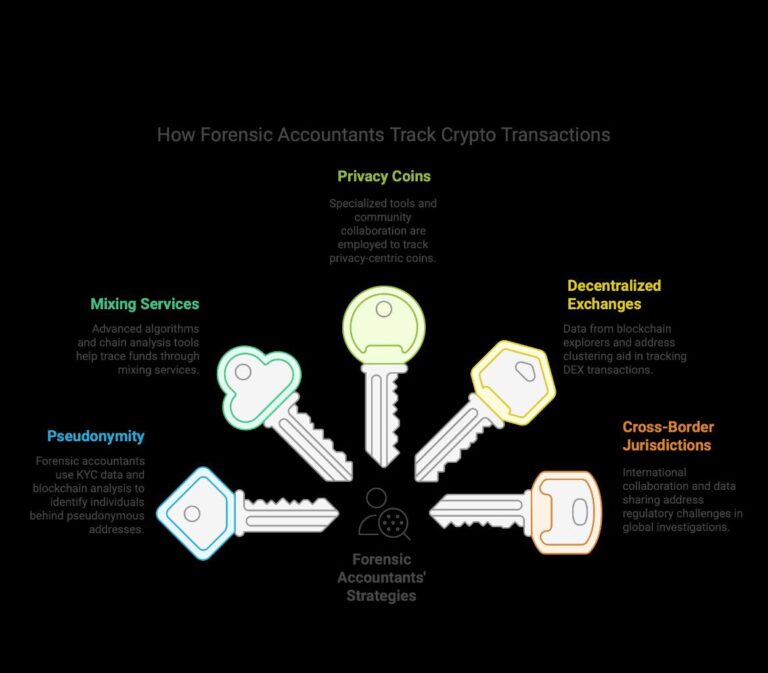
By combining digital evidence, network analysis, and forensic investigation techniques, ethical hackers can identify the individuals responsible for the security breach.
This information allows companies to take appropriate action to protect their systems and address the security incident.
Warning Signs of Corporate Data Breaches
Organizations should remain alert to early indicators of potential cyber incidents. Some common warning signs include:
• unusual employee access to sensitive files
• unexpected system slowdowns or abnormal activity
• unauthorized data transfers
• unfamiliar devices accessing corporate networks
• confidential documents appearing outside the company
Detecting these warning signs early can help minimize the impact of cyber threats.
How Private-Hackers.com Helps Businesses Investigate Cyber Threats
When companies face cybersecurity incidents, professional investigation services can provide the expertise needed to uncover the source of the problem.
Private-Hackers.com offers specialized digital investigation and cybersecurity services that help organizations analyze security breaches and detect insider threats.
Their team provides expertise in:
• digital forensics investigations
• cyber-crime analysis
• insider threat detection
• corporate network security assessments
• recovery of compromised digital data
By using advanced investigative tools and cybersecurity expertise, Private-Hackers.com assists businesses in identifying vulnerabilities, uncovering suspicious activity, and strengthening their security infrastructure.
Best Practices for Preventing Corporate Cyber Attacks
Although ethical hackers can investigate security breaches, prevention remains the most effective defense against cyber threats.
Companies should consider implementing these security practices:
• multi-factor authentication for employee accounts
• regular cybersecurity audits
• employee security awareness training
• encrypted data storage and communication systems
• continuous monitoring of network activity
These strategies help reduce the likelihood of unauthorized access and data theft.

Final Thoughts
Corporate data breaches and insider threats continue to pose significant risks for organizations across many industries. Detecting and investigating these incidents requires advanced cybersecurity expertise and digital forensic analysis.
Ethical hackers play a critical role in uncovering cyber threats, analyzing digital evidence, and helping organizations strengthen their security systems.
For businesses seeking professional assistance with cybersecurity investigations, Private-Hackers.com provides specialized digital forensic services designed to help companies identify vulnerabilities, investigate suspicious activities, and protect valuable corporate information.
With the right expertise and investigative tools, organizations can better understand cyber threats and take proactive steps to safeguard their digital assets.
Frequently Asked Questions
What is a corporate data breach investigation?
A corporate data breach investigation involves analyzing digital systems, networks, and devices to identify how unauthorized access occurred and what information was compromised.
How do ethical hackers detect insider threats?
Ethical hackers analyze employee activity logs, network access records, and digital communication patterns to identify suspicious behavior that may indicate insider threats.
Why do companies hire ethical hackers after a data breach?
Companies hire ethical hackers to investigate the breach, identify vulnerabilities, recover digital evidence, and strengthen cybersecurity defenses.
Can digital forensics identify the source of a cyber attack?
Yes. Digital forensic investigations analyze system logs, network activity, and digital footprints to trace the origin of cyber attacks.
Where can businesses get help with cyber investigations?
Professional cybersecurity investigation services like those offered by Private-Hackers.com help businesses analyze cyber incidents, detect insider threats, and strengthen digital security systems.